Achieve fast, audit-ready compliance with India’s Digital Personal Data Protection Act using Infodot’s integrated cybersecurity and compliance framework.
India’s Digital Personal Data Protection (DPDP) Act has made data privacy a board-level priority. Organizations handling personal data must now implement structured frameworks for consent, governance, and security. However, most businesses struggle with fragmented systems, lack of expertise, and unclear compliance paths.
Infodot simplifies DPDP compliance with a practical, execution-driven approach. We combine cybersecurity, IT operations, and compliance expertise to deliver fast, scalable, and audit-ready solutions tailored for startups and enterprises.
DPDP compliance refers to aligning your organization with India’s Digital Personal Data Protection Act. It ensures that personal data is collected, processed, stored, and shared in a lawful, secure, and transparent manner.


DPDP compliance is not just about regulation. It directly impacts trust, risk, and growth.





















“As our IT support team, Infodot is quite reliable. No matter the size of the issue, we know that when we call or email, we will get a response back from your team. Your commitment to customer service is highly appreciated. Infodot has helped solve a lot of day-to-day IT challenges that were previously creating bottlenecks for us.

“As an early stage start-up, the engineering team was fully focussed on our cloud infrastructure and we lacked time and skill to manage office IT infrastructure. This created many bottlenecks for us – unreliable office internet connectivity, unnecessary expenditures due to lack of regular maintenance etc. Once Infodot took up the upkeep of our office IT infrastructure, we could immediately recognize the value they brought in. New internet connectivity architecture was proposed and implemented by Infodot first. It really helped solving our office internet connectivity issues and made our office network more secure. As a co-founder, I also would like to mention that they are accommodative and they understand an early stage start-up’s financial constraints. We are happy with their services and would definitely recommend them.”
We follow a structured, outcome-focused approach:
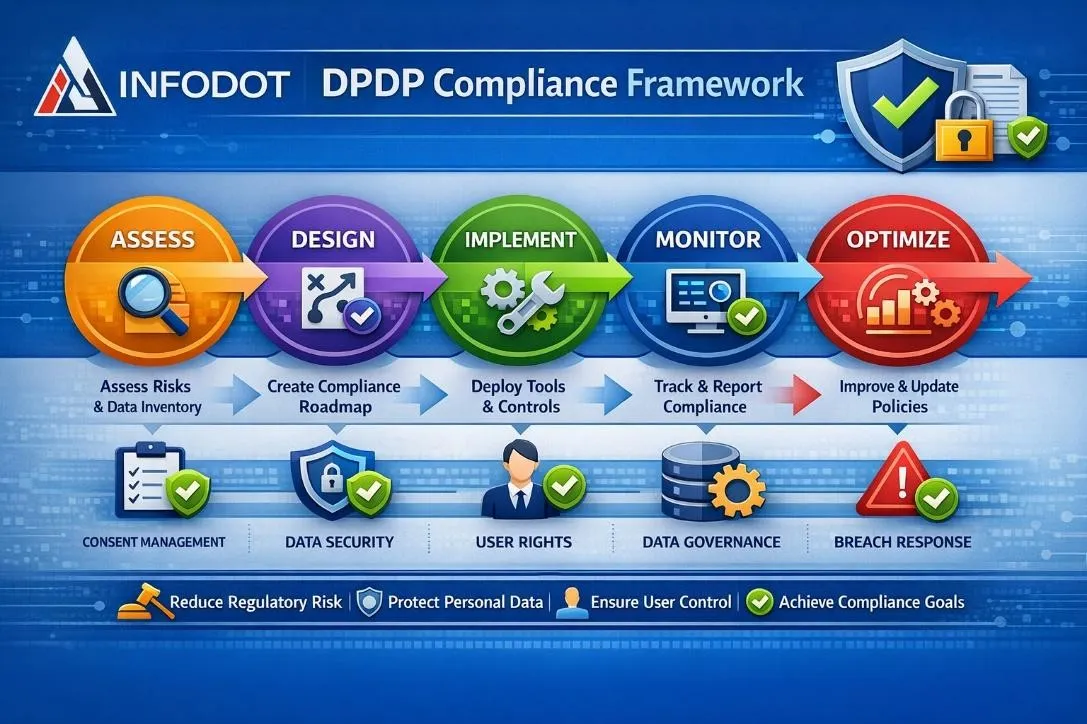
Identify what personal data you collect, where it resides, and how it flows.
Ensure lawful data processing with clear and trackable consent mechanisms.
Establish structured policies and accountability.
Integrate compliance with strong cybersecurity.
Enable compliance with user rights under DPDP.
Ensure your partners are compliant.
Stay prepared for audits and regulatory checks.
Be ready to respond to data breaches.
Get expert compliance oversight without full-time hiring.

Infodot provides a comprehensive range of IT services, including co-managed support, cybersecurity, cloud solutions, and IT consultancy, designed to optimize your business operations.
CERT In Cybersecurity Compliance Services for MSMEs 🚨 URGENT: MSME Cybersecurity Compliance Now Mandatory Effective
Start your journey with Infodot today.
Emergency Hotline: Available 24/7 for incident response
DPDP compliance ensures your organization follows India’s data protection law by managing personal data securely, lawfully, and transparently, while enabling user rights and maintaining accountability.
It helps avoid penalties, builds customer trust, reduces cyber risks, and enables business growth through secure and compliant data practices.
It can take a few weeks for basic setups and several months for full implementation depending on complexity.
Yes, startups handling user data must comply to avoid risks, build trust, and support growth.
Costs vary based on size and scope, typically ranging from ₹50,000 to ₹10+ lakhs.
A Data Fiduciary is an organization or entity that determines the purpose and means of processing personal data. It is responsible for ensuring compliance, protecting data, and respecting user rights under the DPDP Act.
A Data Principal is the individual whose personal data is being processed. They have rights such as accessing, correcting, deleting their data, and withdrawing consent at any time.
Key requirements include obtaining valid consent, implementing security controls, enabling user rights, maintaining data governance, ensuring breach reporting, and keeping audit-ready documentation across all data handling processes.
Consent management involves collecting, storing, and managing user permissions for data processing. It ensures transparency and allows users to control how their personal data is used.
Data mapping identifies where personal data is stored and how it flows across systems. It helps organizations implement controls, reduce risks, and ensure compliance with data protection regulations.
A DPO oversees compliance, manages risks, handles user grievances, and ensures that the organization follows data protection laws effectively and consistently.
Yes, any business handling personal data must comply, regardless of size. Small businesses benefit from early compliance by reducing risks and building customer trust.
Non-compliance can lead to penalties, reputational damage, legal issues, and loss of customer trust. It can also impact business growth and partnerships.
Data minimization means collecting only the data necessary for a specific purpose. It reduces risks and ensures compliance with regulatory requirements.
Purpose limitation ensures personal data is used only for the purpose it was collected for. Any additional use requires fresh consent.
A data retention policy defines how long personal data is stored and when it should be deleted, ensuring compliance and reducing risks.
Secure deletion ensures that personal data is permanently removed and cannot be recovered, preventing unauthorized access or misuse.
A data breach is any unauthorized access, disclosure, or loss of personal data. Organizations must detect, manage, and report breaches promptly.
Organizations must detect breaches quickly, contain the impact, notify authorities and users, and implement corrective measures to prevent future incidents.
Role-based access control restricts data access based on user roles, ensuring employees only access data necessary for their responsibilities.
Encryption converts data into a secure format, protecting it during storage and transmission and preventing unauthorized access.
Vendor risk management ensures third-party service providers comply with data protection standards, reducing risks associated with external data handling.
Audit readiness means maintaining proper documentation, processes, and controls to demonstrate compliance during regulatory inspections or audits.
Compliance monitoring involves continuously tracking systems and processes to ensure adherence to data protection regulations and identify potential risks.
Privacy by design integrates data protection measures into systems from the beginning, ensuring compliance is built into processes rather than added later.
It refers to transferring personal data outside India. Organizations must ensure proper safeguards and comply with regulatory guidelines for such transfers.
Tools include consent management platforms, data loss prevention systems, monitoring tools, and compliance dashboards to manage and track compliance effectively.
By ensuring secure and transparent data handling, compliance builds confidence among customers and strengthens brand reputation.
Yes, many aspects such as monitoring, reporting, and consent management can be automated using advanced tools, improving efficiency and accuracy.
Compliance should be reviewed regularly, typically quarterly or annually, and updated continuously based on regulatory changes and business needs.